Introduction
Securing and monitoring workloads is top priority when working with microservices. Monitoring is a difficult task when done manually. Developers need to configure each service to ensure safe communication within the system. Additionally, they need to monitor the exchanges, which takes time. Time that could have be spent developing the app itself.
Instead, there is a much simpler solution – using a service mesh platform such as Istio.
In this tutorial, you will learn about Istio, its architecture, and how it is used.
What is Istio? – Defining Istio Service Mesh
Istio is an open-source service mesh implementation that manages communication and data sharing between microservices. The platform is added to reduce the complexity of managing network services.
Once installed, it injects proxies inside a Kubernetes pod, next to the application container. Each proxy is configured to intercept requests and route traffic to the appropriate service while applying policies.
Why the need for a service mesh?
Moving from monolithic to microservice architecture, developers get the opportunity to build highly flexible, resilient, and scalable applications within much faster software development life cycles. Although the microservice architecture has many benefits, the evolution in application development also brings certain challenges.
As the architecture consists of many individual services working together, it is important to ensure seamless communication. These autonomous components talk to each other through APIs. However, managing traffic flow and API calls requires a lot of time and effort from the development team.
There was a need for a third-party solution that allowed team members to focus on developing the service logic instead of the network logic. Therefore, service meshes like Istio were designed to manage the network layer of service-to-service communication.
Istio Architecture
The Istio architecture includes two main components:
- Control plane. This component is used for configuring and managing proxies in the data plane.
- Data plane. The second element of Istio includes all sidecar proxies inserted inside the pods.
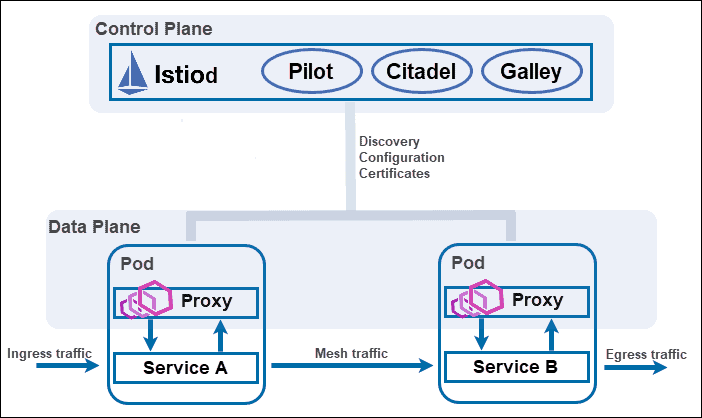
Control Plane
Before version 1.5, the control plane was a cluster of different components – Pilot, Citadel, and Galley. Istio 1.5 introduced Istiod, a control plane that combined the above-mentioned components into one. Istiod simplified configuring and operating the service mesh.
Istio services in the control plane include the:
- Pilot uses the Envoy API to communicate with Envoy sidecars. It is responsible for traffic management, routing, and service discovery.
- Citadel provides secure communication among services by managing user authentication, certificate, and credential management.
- Galley is responsible for configuration management, ingestion, distribution, and processing.
Data Plane
The data plane consists of Envoy proxies deployed into the pods as sidecars. They interact with and manage traffic for all services within the system. This includes controlling all network communication between microservices.
Since they are added as sidecars, there is no need to redesign the application’s architecture to implement the proxies.
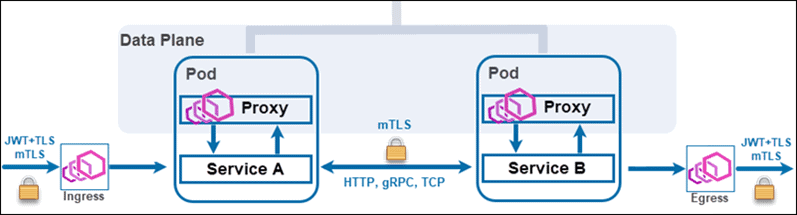
The proxies control traffic by specifying routing rules (for HTTP, gRPC, TCP) and enforcing TLS and traffic encryption.
All traffic goes through the Envoy proxies. Therefore, these components collect large amounts of data and provide valuable insight into your business traffic.
Envoy proxies provide:
- Dynamic service discovery
- Load balancing
- Health checks
- TLS termination
- HTTP/2 and gRPC proxies
- Circuit breakers
- Staged rollouts with percentage-based traffic split
- Fault injection
- Rich metrics
Note: Learn about the importance of continuous testing of microservices.
Istio Features
The platform’s most important features are:
1. Traffic Control
The main feature of Istio is its role in traffic management. It controls the flow of traffic between services by implementing routing rules through its Envoy proxies. By deploying proxies, Istio directs traffic and API calls without making any changes to the service itself. This allows users to perform canary rollouts, staged rollouts, and A/B testing.
2. Observability
The platform controls and observes all incoming and outgoing traffic within the network layer. Therefore, it collects large amounts of data that provide useful insight for future development.
3. Security
While developers secure the application from potential threats and hacks, Istio authorizes, authenticates, and encrypts all internal communication. Pods and services talk to each other and transfer data under Istio’s policies.
Istio Advantages and Disadvantages
To help you decide whether or not to implement Istio into the microservice architecture, take a look at some of its advantages and disadvantages.
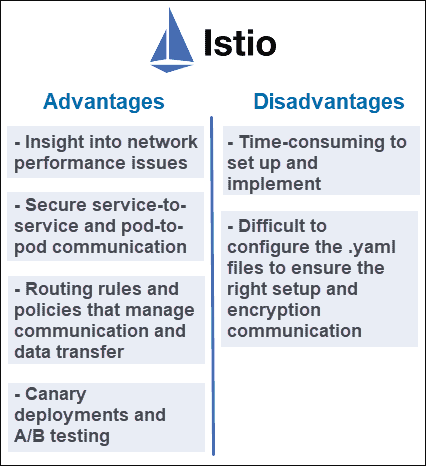
Advantages
- Gives insight into network performance issues.
- Secures service-to-service and pod-to-pod communication.
- Implements routing rules and policies that manage communication and data transfer.
- Enables canary deployments and A/B testing.
Disadvantages
- Istio is time-consuming to set up and implement.
- Also, it is difficult to configure the .yaml files to ensure the right setup and encrypted communication.
Conclusion
After reading this article, you should understand what Istio is and why it is useful. Since it is just one implementation of the service mesh, make sure to research other popular service mesh solutions.