Password Generator
Use the customizations options below to generate a strong password. The slider allows you to specify the password length (between 6 and 50 characters).
Select the types of characters to include:
Your Password:
What Is a Good Password?
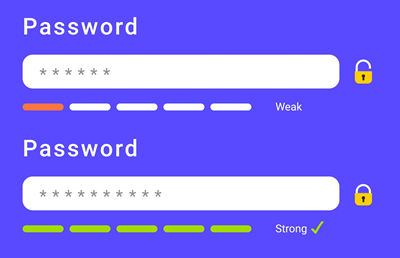
A strong password is a unique, random string of different characters that cyber attackers cannot easily guess or crack. A good password presents a complex challenge to hackers due to its length, randomness, and the use of different types of characters.
The sections below explain what makes a password strong and difficult to crack.
Use Different Types of Characters
A strong password uses different types of characters, such as lowercase and uppercase letters, special symbols, and numbers. The more complex a password is, the more difficult it is for hackers to crack. Conversely, avoid passwords that utilize a single type of character (e.g., 2134535783458).


Use at Least 12 Characters
A safe password uses at least 12 characters, but the longer the better. The easiest way to make a password strong is to use more characters. For example, the password 69@904@8 uses numbers and special characters and is 8 characters long. The estimated time it would take to crack that password is 5 days. On the other hand, the password 6193^^9^4$77 still uses numbers and special characters only but is 12 characters long and it would take a thousand years for hackers to crack it.
The Password Must Be Random and Unique
Every login account must have a unique, random password. Using a unique password for each account makes it harder for cyber attackers to gain access to several accounts. The practice of using random passwords is an additional security layer as they are less likely to be included in lists of commonly used passwords that cyber attackers use first when attempting to break into a system.
What Is a Weak Password?
Your password protection is weak if you:
- Use less than 12 characters for passwords.
- Use the same password for multiple accounts.
- Never change your password.
- Use easily accessible personal information in passwords, such as a family member’s name, date of birth, your pet’s name, favorite sports team, account username, etc.
- Use common words (e.g., MyF@voriteSportsTeam).
- Don’t use different types of characters.
- Use a common sequence of characters (e.g., 12345678910).
If your passwords are based on the practices above, generate a unique strong password using phoenixNAP’s free password generator and update your account credentials.
Password Protection Best Practices
Password protection best practices is a combination of education against phishing attacks, using strong passwords, and using password managers. Use the following best practices to secure your passwords and accounts:
- Change passwords every 2-3 months.
- Never reuse an old password.
- Don’t save your passwords in plain sight, such as an online document, email or not even on a piece of paper.
- Don’t store passwords on browsers. Instead, use password managers.
- Never share your password with anyone. If you must share a password for a shared account, never do it via email or text message. Instead, use a password manager.
- Use multi-factor authentication. No password is foolproof as is no system that stores credentials. Using multi-factor authentication as a secondary security mechanism mitigates the dangers of a compromised password.
Frequently Asked Questions
How Are Passwords Hacked?
Cyber attackers use different ways to steal or hack a password. Brute force attacks involve using every possible combination of characters until the attacker finds a match. This is the most time-consuming and primitive way of cracking a password. Dictionary attacks involve using a list of common passwords, phrases, and words to find a match. Other cyber attacks focus on social engineering tactics to trick users into revealing their passwords. Each type of attack can be at least partially mitigated with a strong, random, and unique password paired with the use of two-factor authentication.
Is It Bad to Save Passwords in a Browser?
Saving passwords in a browser is very convenient and increases security as it motivates users to use strong passwords unique to each account. However, there are inherent security risks to storing passwords in browsers. Firstly, bad actors can access information easily if the workstation is left unattended. Secondly, if malware gains access to the browser, it will potentially access all your saved passwords. Thirdly, storing passwords for sensitive accounts in a browser is not considered good practice.
Can the Same Password Be Used for Different Accounts?
It is not recommended to use the same password for multiple accounts due to the increased risk of it being stolen or cracked. If one of your accounts gets compromised, all of your accounts are easy targets for a cyber attack. While reusing passwords across accounts is convenient, it poses a major security risk each cyber attacker will try to exploit.
Is Multi-Factor Authentication Necessary with Strong Passwords?
Strong passwords are not an unbeatable security mechanism. As with data breaches, it is not a matter if, it is a matter of when one of your account credentials will get compromised. Multi-factor authentication adds another security layer that introduces a secondary authentication process beyond just using a password. Essentially, it mitigates the dangers of a compromised password, as cyber attackers need to bypass several authentication mechanisms.
How Often Should a Password Be Updated?
Update passwords every 60-90 days. While regular password updates minimize the chances of unauthorized access, organizations and individuals should not rely on that mechanism only. It is even more important to always set a strong and unique password.
