Emails continue to be one of the most exploitable attack vectors criminals use to target companies. A single employee opening a malicious link in an email is enough to enable a hacker to bypass all cyber defenses, which is why preventing email-based threats should be a top priority.
This article covers 15 effective yet easy-to-implement email security best practices you should follow to improve your email security. We also go through the most common email-based threats your workforce can face, so read on to learn how to keep would-be hackers out of your company's inboxes.

Best Email Security Practices
Below is a list of the most effective email security best practices you should follow to improve general cybersecurity and ensure your workforce is ready for email-based threats.

Use Strong Email Passwords
The easier the password is to guess, the more likely it is that someone will breach the email account.
Even if you do not rely on a password like "123456" or "password123" (which, unfortunately, too many people do), hackers have access to top-tier brute force attack tools that can crack even moderately complex passwords. For example, a password like "Pa$$word2211991" may look secure, but a high-end tool could crack that password in under a minute.
Each staff member in your company should have a solid and unique password for their email account to prevent brute force attacks (or someone simply guessing the password). A reliable password should:
- Have at least 12 characters.
- Rely on a mix of upper and lowercase letters, numbers, and special symbols.
- Be random and unique.
- Not include common phrases.
- Not contain any personal info (names of family members or pets, companies, places of birth, birthdays, or any other info a hacker can discover by googling your name or spying on social media).
Our article on strong password ideas presents 11 methods for coming up with reliable yet easy-to-remember passwords.
Prepare for Phishing Emails
A phishing email attempts to trick one of the employees into either providing helpful info or clicking on a malicious link. An attacker typically uses phishing to scam the target into:
- Downloading malware.
- Providing sensitive data (typically login details).
Phishing tactics are among the most common social engineering methods criminals use to exploit emails. Some of the standard strategies include:
- Pretending to be a service provider and asking the target to "log in" via a link that leads to a fake website.
- Imposing a superior and asking for sensitive data.
- Pretending to be a part of the security team and asking the victim to "update" one of their passwords.
- Sending an email with a malicious file that has a hidden program.
Unfortunately, there is no way to stop phishing emails. Your employees are bound to receive one from time to time, which is why educating the workforce is the primary way to protect your company.
The golden rule of preventing phishing is to not respond to, click links, or open attachments in emails that look suspicious. Employees should use common sense before interacting with an email and must be able to:
- Recognize suspicious files and links.
- Assess the reasoning behind the request within the message.
- Inspect the sender's address.
- Assess the general state of an email (grammar, business context, the tone of voice, the lack of an email signature, etc.).
You can also run regular phishing simulations to keep employees alert and test their real-life ability to identify suspicious emails.
Learn about spear phishing, a highly targeted type of phishing that focuses on tricking a specific employee instead of going after as many victims as possible.
Use 2FA to Verify Email Logins
Two-factor authentication (2FA) requires an employee to provide an additional credential besides typing in a username and password. Another verification factor adds an extra layer of defense and is a vital counter to brute-force attacks and password cracking.
Besides providing a username and password, 2FA requires the employee to provide one (or more) of the following:
- A unique item (token, card, etc.).
- A PIN received via SMS, email, voice call, or a time-based one-time password (TOTP) app.
- Biometric data (eye, fingerprint, face, or voice scans).
- A barcode generated on a mobile device.
- A prompt on a mobile phone that confirms the user is currently trying to log in.
Even if an attacker steals the email credentials of one of your employees, the use of 2FA will prevent the intruder from logging in to the email account.
Luckily, deploying 2FA is not as technical as it sounds. Most email platforms offer two-factor authentication by default, so there is no reason not to use 2FA to protect your company's inboxes.
Train Employees on How to Handle Email Attachments
Attackers typically use email attachments to hide executable files or programs that inject malware into the system. Before opening an attachment, educate your employees to ask themselves the following questions:
- Is the sender someone within my organization or someone I can trust?
- Is the format right for this type of attachment (look out for .exe (executable program), .jar (Java application program) and .msi (Windows Installer))?
- Does the email itself mention anything about an attachment?
- Am I expecting this email attachment?
- Is the sender's address legit?
- Is the person behind the attachment sending your emails regularly?
If there is even the slightest doubt, the employee should not open the attachment. Instead, they should first confirm the content with the sender to make sure that the email is real.
You can also use endpoint email security to aid your employee's battle with malicious files. These tools include anti-malware and virus programs that scan email content for dangerous links and attachments.

Ensure Employees Never Access Emails from Public Wi-Fi
If you allow employees to take office devices home or open work emails from personal devices, you must ensure workers do not access emails on public Wi-Fi.
A cybercriminal only needs basic skills to discover data passing through publicly accessible Wi-Fi, so both sensitive data and login credentials are at risk.
Employees should only access their email when they are confident in network security. A much safer option (although not as secure as opening emails only when using office Wi-Fi) is to use mobile internet or internet dongles for out-of-office use.
Ensuring employees do not use public Wi-Fi is only a single aspect of your Bring Your Own Device security strategy. Our article on BYOD policies explains what else you need to cover.
Have Periodic Password Changes
One of the simplest (and most effective) email security best practices is to ensure employees change their passwords regularly. You should:
- Ensure each worker has a new email password every 2 to 4 months.
- Use devices to force password changes instead of leaving it up to employees to update credentials.
- Prevent employees from adding one or two characters to the current password to create a new one.
- Prevent workers from using passwords they already had in the past.
Of course, each new password should follow the standard rules for strong passphrases (mix of lower and upper cases, numbers, symbols, etc.).
Never Give Away Personal Info in an Email
If an email asks you for any personal info (birthday, social security number, credit card number, password), the chances are that the message is a scam.
If an email asks for private info, you should call the company in question by finding their contact info online and not by following the instructions in the email. In all likelihood, you will discover that the company knows nothing about the email, and they will caution you not to send private data over email.
Never Reply to Scammers and Spammers
Some employees like to respond to phishing emails and spam messages, but you should ensure workers do not reply to scammers.
Sending a response to a scammer or spammer verifies that your email address is valid. While there is no immediate danger, letting a scammer know that you use that address opens the door to more attacks in the future.

Train Employees to Check Email URLs
Another simple but effective email security best practice is to train employees to inspect URLs when they get a link within an email (especially when the message comes from an unfamiliar source).
Before clicking on a URL, the employee should hover the mouse over the link. If the address does not contain the HTTPS extension, the chances are that the URL does not lead to a safe website. Scammers often try to lure a victim into clicking on a link that leads to a download page for malware. These unsafe websites typically have the HTTP extension.
Also, the URL may look like a familiar link, but is it? For example, a scammer can replace one domain letter to fool the employee into thinking the URL is legitimate (such as goggle.com instead of google.com).
Do Not Reuse Passwords Across Accounts
Every employee should have a unique password for every account. Their email password should not match any passphrase they use for other purposes (backend logins, tool credentials, HR software passwords, etc.).
The match between passwords also applies to private accounts. For example, a worker's Facebook or bank account password must not be the same as their credentials for work email. That way, if the bank's credentials were ever a part of a data leak, your company's email account would not be in danger.
Since having a unique password for each account is among the most tedious email security best practices, you should use a password management tool like 1Password or LastPass. These platforms automatically create complex passwords and store them while an employee only needs to remember one master password.
Here are 11 password management solutions you can use to simplify everyday operations and protect your company from unsafe and reused passwords.
Use a Spam Filter
Most email services providers have a built-in spam filter. A filter helps:
- Separate legit emails from malicious messages.
- Lower the likelihood of phishing and spamming.
- Keep the inbox tidy and more manageable.
As an added benefit, a spam filter makes the number of emails less overwhelming. Employees will be more focused when navigating their inboxes and alert to suspicious messages.
While most associate spam with onslaughts of ads, a spam message can also contain malware or, even worse, ransomware. If a spam filter stops a ransomware email from entering an employee's inbox, turning the feature on was worth the effort.
Wish to learn more about ransomware? Check out these articles:
- Ransomware Examples
- How to Prevent Ransomware: 18 Best Practices
- Linux Ransomware: Famous Attacks and Protection Guide
- Terrifying Ransomware Stats and Facts
PhoenixNAP's ransomware protection services can help you counter this cyber threat with immutable backups and strategic disaster recovery measures.
Prevent Employees from Using Business Emails for Private Purposes (or Vice Versa)
Workers should use business emails only for company-related issues and updates. There is no reason for an employee to:
- Use the email for private purposes (such as subscribing to newsletters, making gaming accounts, etc.).
- Send work-related stuff to a private email address.
- Shop online with a professional email.
- Use the address to exchange personal messages.
- Post the address anywhere online (social media, forums, chat rooms, etc.).
Whenever an employee shares their email, they increase the chance of the address falling into the wrong hands. Hackers scan public websites to collect info they sell or target later, so every exposure of the address adds risk.
Another reason for stopping an employee from sending work-related stuff to a private email is that anyone who hacks the personal address (which is likely not as protected as a company email) will have access to whatever the employee sent from the business address.
Educate Employees About the Value of Email Security
Educating employees instead of just enforcing email security best practices is vital. Without awareness building, an employee might perceive demands for complex passwords and strict rules as pointless and unjust.
You should organize mandatory email security awareness sessions that explain:
- All relevant email security best practices.
- The latest trends in email-based attacks.
- How to recognize signs of phishing.
- The importance of using work emails only for job-related purposes.
- How to inspect email addresses.
- The traits of legitimate and illegitimate email requests.
- How to create strong passwords.
- Where employees can find the company's email and password-related policies.
- How employees should react to suspicious emails.
No matter how many security measures you deploy, spam and phishing emails will occasionally fall through the cracks. When they do, your workforce's understanding of email threats is what makes the difference between a failed and successful breach attempt.
Our article on security awareness training offers tips and tricks for getting the most out of any educational program you are preparing for your workforce.
Ensure Employees Log Out of Email Accounts at the End of the Day
Another effective yet simple email security best practice is to ensure employees log out of their email platforms at the end of the workday. You can encourage workers to log out on their own, or you can use the email platform to log everyone out at a particular time automatically. This practice is beneficial when an employee uses an unfamiliar device or a network to check their email.
Use Email Encryption
Every email is at risk of being intercepted by an attacker or going to the wrong address. You can use data encryption to counter both threats.
Encryption scrambles the original email content and turns the message into an unreadable mess. The recipient can reveal the text with a unique decryption key, so any in-transit interception or a wrong recipient cannot lead to a data leak.
Our article on encryption at rest explains the basics of using cryptography to protect data from unauthorized users.
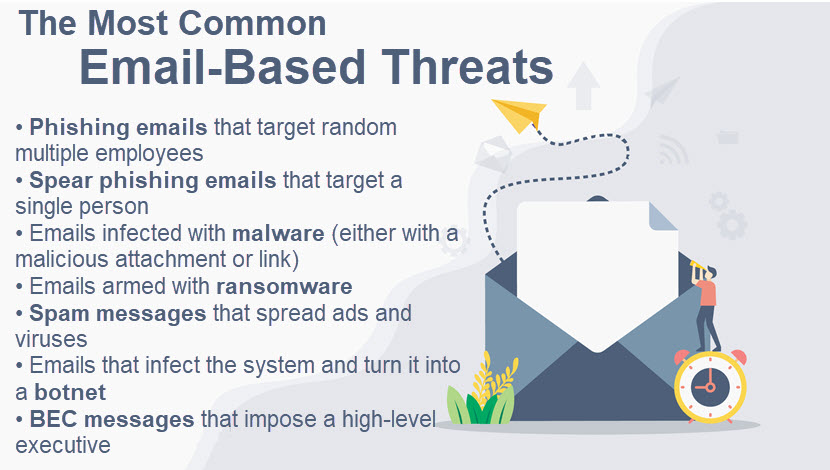
Common Email Security Risks
Unfortunately, there is no shortage of email-based threats. Some of the most common email security risks you can encounter are:
- Social engineering emails: Social engineering tactics attempt to earn the target's trust to steal info. Phishing is by far the most common email-based social strategy.
- Malware-armed emails: These emails try to inject malware into your system. The attacker typically "arms" the malware in an attachment or on a fake website the victim is supposed to open. If the malware makes it into your system, the attacker can take control of devices, steal data, or set up spyware.
- Spam: Spam involves various unwanted messages that can overwhelm an inbox with ads and trojan-infected messages. As around 60% of the world's email traffic volume is spam, you should not overlook this threat.
- Ransomware: If a malicious email contains a ransomware program, a single employee opening the wrong email can enable an attacker to encrypt your data or devices.
- Botnet messages: An infected email can turn your company's devices into a part of the botnet used to target other victims with DDoS attacks.
- Business Email Compromise (BEC): A BEC is a type of spear phishing in which a hacker pretends to be one of the company's high-level executives.
Unfortunately, cyberattacks (email-based and otherwise) are constantly evolving, so staying ahead is challenging. Hackers can be very clever and creative, so protecting your company's inboxes requires keeping up with the latest threats.
Signing up for our monthly newsletter will ensure your team stays up to date with both the latest cybersecurity dangers and the security strategies to counter those threats.
Use Email Security Best Practices to Keep Your Team's Inboxes Safe
A single malicious email can be enough to enable an attacker to bypass your company's entire security strategy. Luckily, the email security best practices above will improve resistance to email-based threats, so start protecting your company with a mix of proactive measures and timely employee education.



